Keys & Locks
That Talk
Do you want the knowledge and control of who is coming and going in your busy workplace?
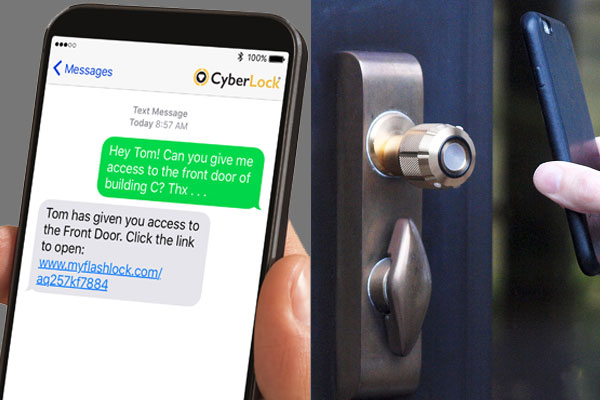
Imagine if the keys & locks in your company could talk to you! If you could control who went where and at what time, received regular information updates and changed the access privileges at the click of a button.

Control when
You Need It Most
With a fully supported software integration for audit trail and adding or deleting of keys remotely, CyberLock is an easy to use custom-designed electronic key system that can suit any application cost-effectively.
No Wires, No Power, replace the existing cylinder and in an instant, you now have Access Control to a single door or 1,000’s of doors or even padlocks, which can stand alone or be software-driven.
When a CyberKey meets a CyberLock
an instant information exchange determines whether the key has access to that specific lock. Whether access is granted or denied, the time of the event and the unique ID of the key used is stored in both the lock and the key.


CyberLock cylinders are the exact dimensions
of the normal lock cylinders they replace. The absence of a conventional keyway means it is not vulnerable to being picked. As the CyberLock cylinder needs no power or wiring it’s ideal for remote and mobile assets.
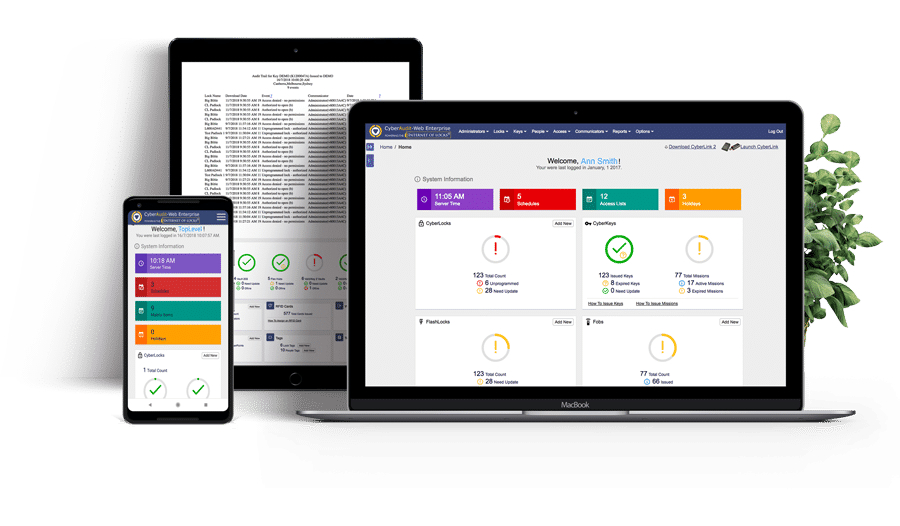
Centralised, web-based software
allows facility managers to assign keys, set access permissions and expiry times. They can also create access groups and schedules, and activate new EKA locks. It also enables auditing and tracking through reports and automatic notification of suspicious activities.
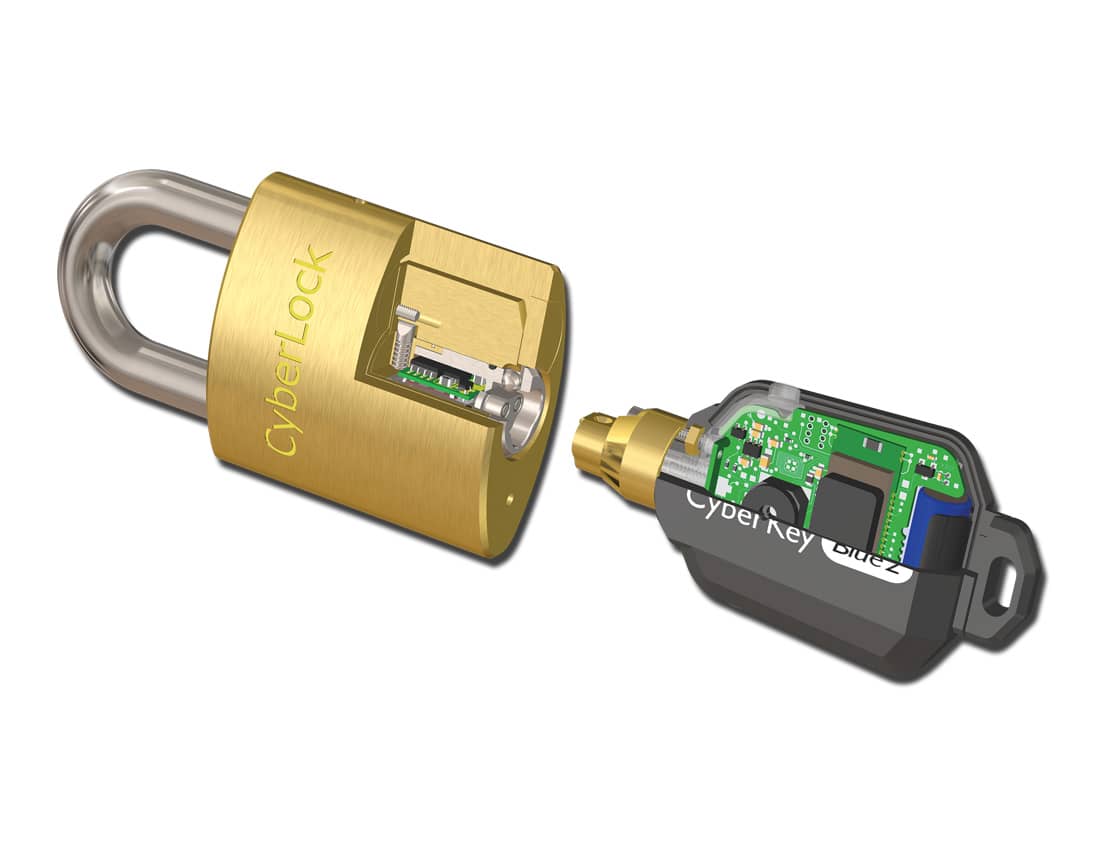
Each CyberKey contains a battery
and the individual’s access privileges. This powers all the electronics and operates the lock. For example, the key can be programmed to allow access from 8 am to 6 pm on weekdays and 10 am to 4 pm Sundays. It can even be programmed to expire so it cannot function until reactivated.
Access privileges are distributed
through communicators linked to your EKA software via network or internet. When validating keys, the system downloads the key’s stored data for audit. It then uploads any new access privileges. EKA access privileges can be programmed to expire. This forces users to update keys regularly.

Through a hub called Flex
EKA is able to integrate with and manage any other access control system that uses a Weigand — compatible input device-from RFID, to electronic swipe and HID, Maglocks electronic strikes, and even bio-metric devices.
Over 300 existing
CyberLock Designs
CyberLocks are the exact dimensions of the mechanical cylinders they replace. They retrofit into the lock hardware with the ease of a mechanical cylinder and do not change how the lock operates.
More than 300 existing CyberLock designs enable it to be installed in an enormous variety of interior and exterior doors, padlocks, containers and cabinets. There’s no wiring and no battery. All power is provided by the CyberKey: when a key comes in contact with the cylinder, it powers up the lock’s circuitry so key and lock communicate. If the key is not on the lost key list and the permissions are correct, the lock will open.
The circuitry stores four types of information: encrypted codes that ensure only keys within the system work with the lock; the unique ID number of the CyberLock; a record of the last 1,100 entries; and a list of lost keys to eliminating access by any key that is missing or lost.
CyberLocks offer superior physical security. They have no conventional keyway that is vulnerable to being picked plus a tamper plug prevents the lock from opening if the front of the cylinder is struck.
Moreover, if torque is applied to the cylinder, the front part separates from the back half. The back half of the cylinder expands, causing a braking effect that engages the sides of the cylinder’s case, stopping the rotation and leaving the cylinder in the locked position.
CyberLock
FAQs
CyberLock is a customised electronic key system that makes managing your security easy and cost-effective. You have a key programmed to work with a specific lock, and the supporting software allows you to add or delete keys remotely. To adjust the lock, replace the cylinder, and you can control any compatible lock. You do not need to worry about wires or external power sources.
All CyberKeys contain batteries as a power source for the electronic components. Additionally, every key holds the user’s programmable access privileges. You can program individual keys to limit access for specific people. For example, office staff may have keys that operate from 8:00 am- 6:00 pm, but maintenance workers’ keys are programmed to allow admittance 24/7.
The CyberLock and CyberKey exchange digital information that determines if access is granted to the key holder. The lock and key catalogue every entry or attempted entry by using the unique key ID.
The cylinders for the CyberLock are the same size as the ones they are replacing, so the fit is flawless. The fact that there is no space to insert a key prevents picking the lock, which enhances the security of the CyberLock.
More
Services
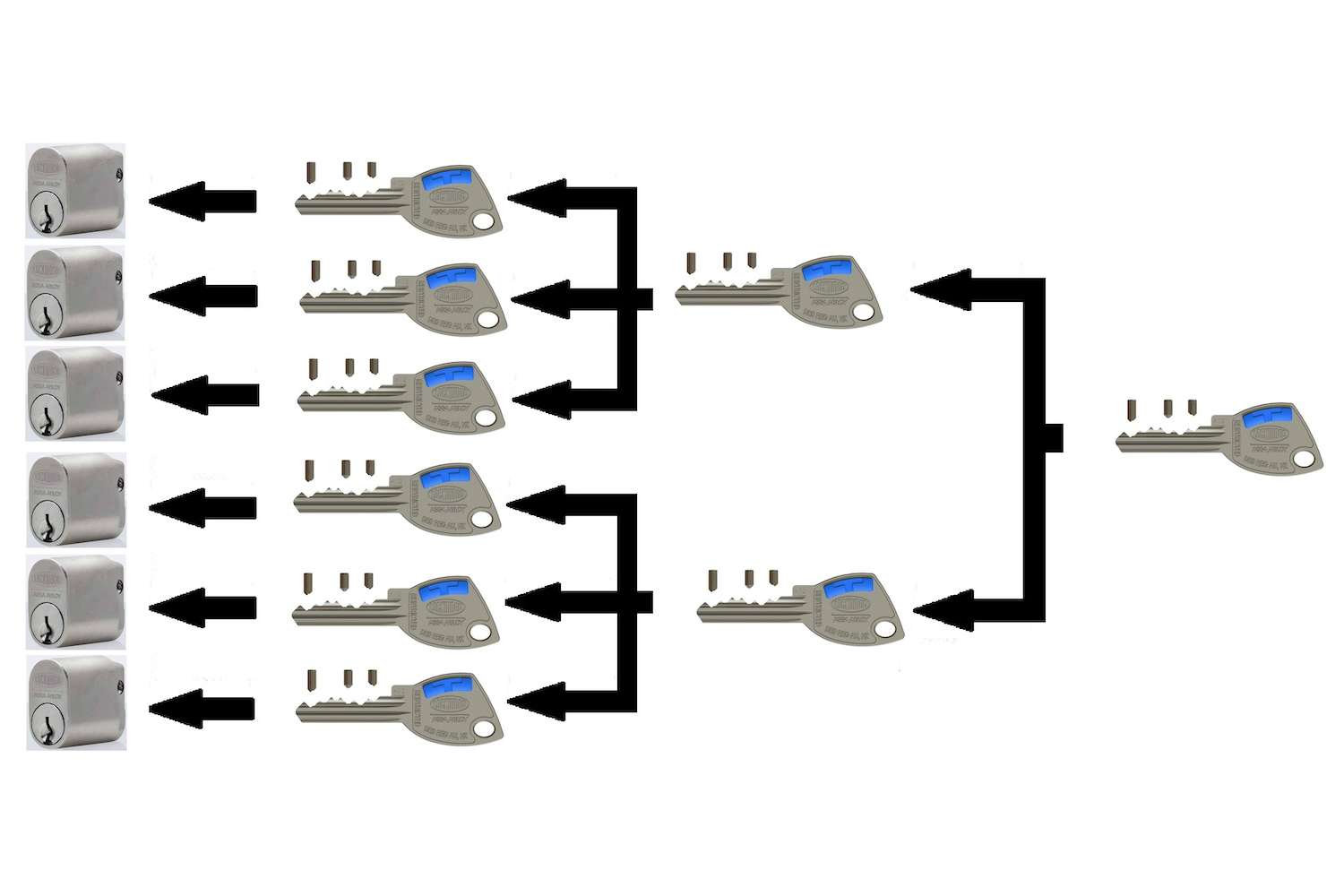
Master Key Systems
Used by businesses, schools and organisations to allow employees access to specific areas as they are…

Aperio by Lockwood
This new technology enables mechanical locks to be wirelessly linked to an existing system.

Salto Wireless Systems
A huge range of access control applications, you choose the level of security control you need!
